What is Vulnerability Management Service?
Vulnerability management service refers to the process of discovering, classifying, prioritizing, remediating, reporting, and responding to software and network security vulnerabilities. Identified vulnerabilities may be remediated in several ways, including patching, software reconfiguration, or security policy updates.
A security vulnerability is a flaw, weakness, or error found within your security program that could be leveraged by a bad actor to compromise your network.
Holistic Vulnerability Management Services
In today’s ever-evolving threat landscape, organizations need robust cybersecurity measures to protect their sensitive data and systems. Vulnerability Management as a Service (VMaaS) offers a comprehensive and proactive approach to identifying, assessing, and mitigating vulnerabilities within an organization’s IT infrastructure. At ITsecura, we specialize in providing VMaaS solutions to help small and medium-sized organizations enhance their cybersecurity posture.
Our highly skilled cyber security specialists offer holistic vulnerability management services, including:
- Vulnerability Scanning: We conduct regular scans of your network, systems, and applications to identify vulnerabilities and potential entry points for attackers.
- Vulnerability Assessment: Our experts assess the severity and potential impact of identified vulnerabilities, prioritizing them based on the level of risk they pose to your organization.
- Penetration Testing: Through simulated attacks, we identify weaknesses in your systems, networks, and applications to proactively address any security gaps.
- Remediation Guidance: Our team provides detailed recommendations on remediating vulnerabilities and strengthening your security infrastructure.
- Continuous Monitoring: We offer ongoing monitoring and vulnerability management to protect your systems against emerging threats.
Why do you need Vulnerability Management?
From neglected software security updates to misconfigurations to weak identity and access management and other instances, there is an entire ecosystem ripe with weaknesses. These vulnerability factors increase the overall risk to an organization.
Attackers can steal data and damage critical systems, which opens the door to potential legal, financial, and public relations challenges. Many organizations every year suffer colossal payouts due to ransomware and the associated fallout. They lose millions over a vulnerability that was not managed appropriately.
To avoid such outcomes, organizations need to take a proactive approach to their vulnerability management and implement continuous vulnerability management programs.

YOUR BENEFITS FROM OUTSOURCING VULNERABILITY MANAGEMENT SERVICES
Formal vulnerability reports
Know your vulnerabilities through the formalized process.

Increase trust with clients
Give your clients confidence that their data is protected.

Continuous Protection
Bi-weekly or monthly scanning gives you reassurance.
Cost effective
Gain greater operational efficiency while minimizing your costs.
Integrates with patching program
A patching cycle is triggered by discovered vulnerabilities.
Remediation guidance
Get guidance when you need it.
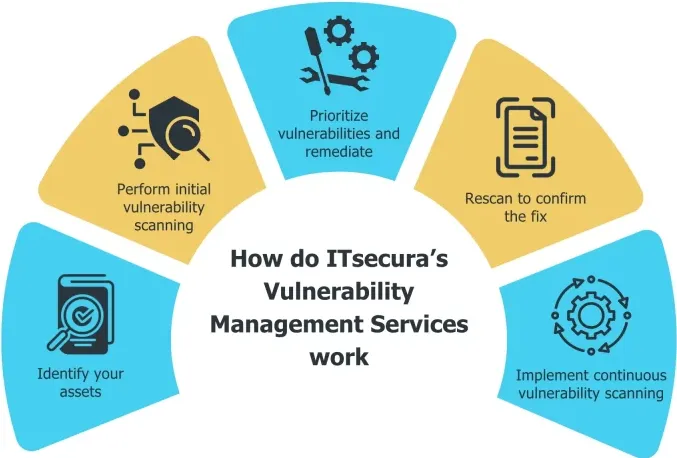
How do ITsecura’s Vulnerability Management Services work?
WHY CHOOSE ITSECURA FOR VULNERABILITY MANAGEMENT SERVICES?
Experience and Expertise
Proven track record over 15 years.
We take it personally
We take responsibility for protecting your business.
Multiple vulnerability scanners
We can scan your servers with as many scanners as needed.
Client-Centric Approach
To meet specific needs and requirements aligned with your goals.
Risk-based prioritization
We consider asset classification during prioritization.
Frequent scanning
A Swiss-inspired systematic approach to regular proactive scanning.
Ready to Hire Vulnerability
Management Experts?
Discover and manage your vulnerabilities proactively. Think strategically!
Frequently Asked Questions
How often should vulnerability scans be performed?
Vulnerability scans should be performed regularly, ideally bi-weekly or at least monthly, to stay ahead of emerging threats.
How does vulnerability scanning differ from penetration testing?
Vulnerability scanning identifies vulnerabilities, while penetration testing simulates real-world attacks to test the effectiveness of security measures.
How long does it take to remediate vulnerabilities?
The time to remediate vulnerabilities depends on their severity and complexity, but prompt action is crucial to minimize the risk of exploitation.
Can vulnerability management services help with compliance requirements?
Yes, vulnerability management services assist organizations in meeting regulatory and compliance requirements by identifying and addressing security vulnerabilities.
How does continuous monitoring enhance vulnerability management?
Continuous monitoring ensures that vulnerabilities are promptly identified, enabling proactive remediation and reducing the window of opportunity for potential attacks.
Are vulnerability management services suitable for small businesses?
Vulnerability management services can be tailored to small businesses’ specific needs and budgets, providing essential protection against cyber threats.