WEAKNESSES


Cyber Security Consulting Services + vCISO Services
Why is Cyber Security necessary?
Nowadays, hackers are attacking everything reachable through the internet, but most people are not aware of how bad the situation is. It takes some effort even to see cyber attacks and takes even more effort to stay protected from them. We have many years of experience blocking hackers and protecting digital assets from cyber attacks with our highly skilled team of cyber security specialists. We can advise you on the most appropriate cyber security measures and help you to implement them.
Build security into the fabric of your digital enterprise. Our industry-leading security solutions and cyber security consulting services will help you detect and block attacks, proactively respond to threats, ensure compliance, and protect data, applications, infrastructure, and endpoints.
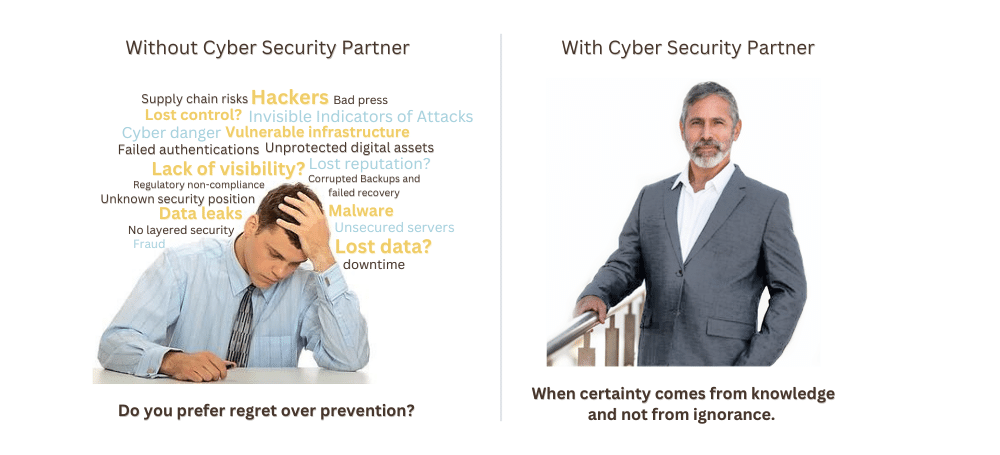
Why do you need a Cyber Security Partner?
CYBER SECURITY CONSULTING FEATURES
How our cyber security specialists can help YOU:
Strategic Security Advisory
We implement business-aligned strategies to optimize your security.
Security assessment
Data and assets classification, risk assessment, controls and processes.
Security Risk Management
We help identify your cyber risks and carry out your remediation projects.
Vulnerability scanning
We can perform vulnerability scans and help you with fixing them.
Data encryption
Data encryption in storage and in transit with strong ciphers.
Network, Server and Endpoints
Advanced threat-protection solutions for your infrastructure.
Security awareness programs
Educate your employees and technical staff about security threats.
Identity and Access
From provisioning and access governance to strong authentication and PKI.
Security Operations Center
We keep your information safe by monitoring operational logs 24x7.
Maximize your business with our Cyber Security Consultancy Services
ITsecura’s cyber security consulting services will help your business to improve its security posture. These services can be used to assess a company’s current security risks, identify vulnerabilities, and develop and implement security solutions.
Our services can help your businesses with a variety of tasks, including:
- Risk assessment: Identifying and assessing the security risks that a business faces.
- Vulnerability assessment: Identifying and assessing the vulnerabilities in a business’s IT systems and infrastructure.
- Security policy development: Developing and implementing security policies and procedures.
- Incident response planning: Developing and implementing plans for responding to security incidents.
Cyber security consultancy services can be a valuable asset for businesses of all sizes. By partnering with us, your businesses can gain the expertise and resources they need to protect themselves from cyberattacks.
9 Steps to build your Cyber Security Posture
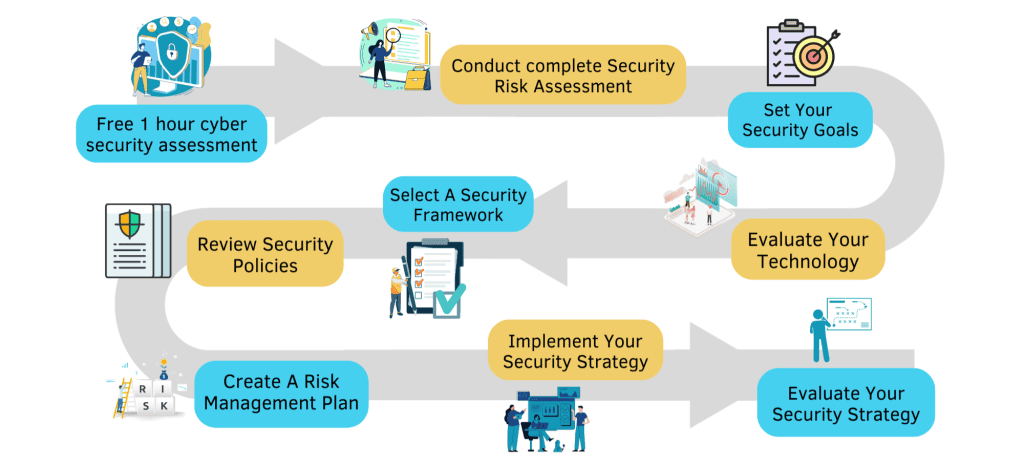
We Are With You Every Step.
Get Started Easily.
Improve your Cyber Security & Think strategically!

Frequently Asked Questions
Why do I need cyber security?
Cyber security is crucial because it safeguards all types of data against theft and loss. Sensitive data, protected health information (PHI), personally identifiable information (PII), intellectual property, personal information, data, and government and business information systems are all included.
- Increased exposure to attacks on organizations.
- Increased Cyber security threats are faced by individuals.
- Cybercrime is expensive.
- Newer hacking methods.
- Hackers are Everywhere.
What does a Virtual CISO do?
A virtual CISO is an assigned resource with experience building and improving information security programs. Starting with a risk assessment, a vCISO first gets an understanding of the strengths and weaknesses of an organization’s security program. Based on the results, the vCISO then works with executive leadership teams to understand goals, budget, and bandwidth—allowing them to provide actionable recommendations, or a roadmap, based on the business’s goals and the risk assessment’s findings. With the roadmap in place, they work with the organization’s internal security team to train staff and make the recommended improvements, improving the ability of the organization to protect its sensitive information and increase its operational efficiencies. Over time, they simply become a sounding board for the organization’s staff to bounce questions and challenges off of.
What is CISO as a service?
CISO as a service is another name for virtual CISO consulting services. ITsecura assigns organizations a certified information security professional to help organizations protect sensitive information and develop cyber security programs.
Where do I get started with cyber security?
Risk assessment is the very first stage of any good cyber security plan. Examples of business risk assessments include compliance assessments, external/internal vulnerability assessments, penetration tests, and social engineering tests.
Does ITsecura offer emergency cyber security services?
Yes, we are available 24/7. We can start helping you before, during, or after an incident. It is much preferable to get involved way before a security incident so that the organization can be ready for recovery and avoid security incidents altogether. Contact us through the Support page https://itsecura.com/support/
What are the benefits of vCISO vs CISO?
CISOs are very expensive. Our vCISO services offer a fractional CISO to lower the cost. A vCISO engagement depends on your business’s size and needs. But, most of the work is preliminary, so the involvement (and therefore the cost) decreases over time. Extensive Industry Knowledge and Skill Does your “security” person wear a ton of hats in the organization? It’s not uncommon for companies to assign security roles as a secondary function to an employee’s primary role. Because of this, they’re often not true experts. A virtual CISO is going to be able to enhance the internal capabilities of your employees tasked with handling security through the techniques they’ve learned.
Why choose ITsecura?
Get peace of mind about your organization’s ability to securely maintain uninterrupted business operations despite the evolving threat landscape – before, during, and after an incident. ITsecura has years of experience blocking hackers and protecting Web Applications used by many top Fortune Companies. Our Cybersecurity specialists are professionals who have expertise in the field of cybersecurity. They can work in a variety of roles, including security analysts, security engineers, and security architects to help protect your organizations from cyberattacks.
For more useful information read our blogs: https://itsecura.com/blog/